Overview

Emails are becoming ever more important, but they have a problem, SPAM.
Receiving unwanted emails that could be scams or viruses, having the emails we send getting stuck in a spam folder, or having fake emails that say they are from us sent to customers / friends / family that are fake invoices or scams, are three key areas being worked on to help fix the spam problem.
There are three tools that are being more popularly used to help fix this; SPF, DKIM, and DMARC.
Secure Email Encryption

Firstly we support email encryption to protect your emails during delivery. A SSL (Secure Sockets Layers) certificate verified by Let's Encrypt Authority X3 provides a public key that email software uses to encrypt the message being sent to you. The corresponding SSL private key is kept secure on the server. Only the server with the private key can decrypt the emails being sent.
This keeps your messages private and safe from others intercepting them on the internet, protecting user names, passwords, personal details, and other sensitive information that's often found in emails.
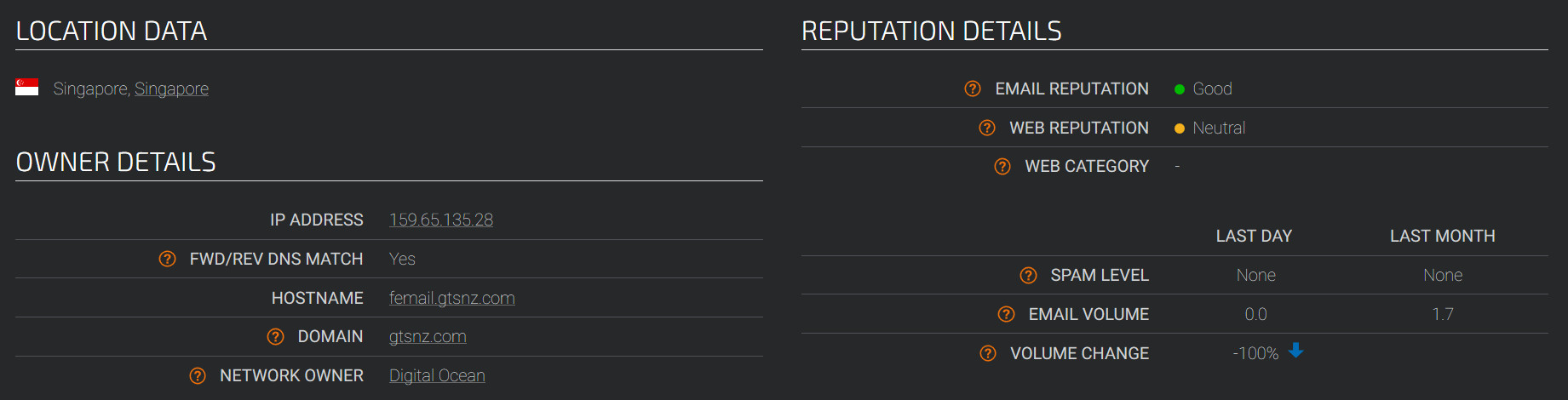
If you are an existing customer looking for the details to connect a new email client to our server, set the incoming mail server to femail.gtsnz.com using IMAP secured by STARTTLS on Port 143, and set the outgoing mail server to femail.gtsnz.com using SMTP secured by STARTTLS on Port 587.
You will need to authenticate both outgoing and incoming connections using your full email address and password.
SPF, DKIM and DMARC
SPF, DKIM, and DMARC are spam filtering tools to help reduce the spam received, to help your emails to pass through spam filters, and to help reduce the chance of spammers being able to send spam email that appears to be from your e-mail address.
All three of these tools use DNS entries for your Domain Name. GTSNZ creates these entries for its customers. Alternatively the required information can be provided to customers who wish to manage their own DNS.
SPF, Sender Policy Framework

SPF, Sender Policy Framework is a DNS record specifying which computers are allowed to send emails. Authenticating your sent emails through our mail server not only enables you to continue sending emails if your connection changes between mobile data and WiFi, it lets us specify that email coming from any mail server that is not the one you authenticate to will be SPAM as it is not you who sent it.
DKIM, Domain Keys Identified Mail

DomainKeys Identified Mail (DKIM) affixes a digital signature to each email sent to guarantee that parts have not been modified since it was sent.
DKIM signed emails are much less likely to get stuck in spam filters as a valid signature verifies trustworthiness of a message. Authenticating your sent emails through our mail server attaches this signature to your sent emails.
While this signature is not usually
visible to end-users, it allows email infrastructure to detect forged
sender addresses, to detect forged recipient addresses, and to detect
changes made to the date and / or subject since the email was sent.
DKIM signatures are verified by checking them with a DNS entry specifying the public DKIM key.
DMARC, Domain-based Message Authentication, Reporting and Conformance

DMARC specifies what should happen to messages that fail SPF or DKIM, and provides for reporting.
DMARC reporting lets you see reports of where emails are being sent that have a from address at your domain, when sent to DMARC enabled servers. You can see your legitimate messages and see how many fraudulent messages are being sent, and where from.
For example you will see reports from companies like Google and Amazon
showing valid emails that you have sent to accounts there. DKIM DMARC
will be aligned and SPF DMARC will be aligned in the report.
You may also see reports from where people have tried to use a fake from address at your domain. Sometimes spammers do this to try to get you to open the mail. Maybe they will even pretend to be you when sending you a message. The report will show DKIM DMARC fail and SPF DMARC fail.
There are three modes that can be specified for DMARC; monitoring, quarantine, and reject. In monitoring mode the reports will let you see that the DNS entries are working. When your emails are showing they are being identified properly DMARC can be changed to either quarantine or reject mode. Quarantine mode instructs mail servers that receive mail from your domain that does not pass the tests, to be placed in the spam folder. Reject mode is similar to quarantine mode, except that it instructs mail servers that receive mail from your domain that does not pass the tests to reject the mail.
Email Reputation
Email Reputation can take a while to get established. As an email-server shows over time that it is not sending spam it gains more trust for sending emails.
GTSNZ communicates with other email providers to help build the trust of the mail server for legitimate emails.
Cisco Talos Intelligence has started to list the email reputation of our email server as good. They have given us the best score out of three possible scores; poor, neutral and good.
GTSNZ Email Policy - Permission
As we are a responsible email service provider we abide by and require our clients to honour "Permission" email practices:
- "Permission" means that the recipient has chosen to "opt-in" to receiving the email.
- If it's important to allow people to opt in, it's just as important to give them the opportunity to opt out or "unsubscribe" whenever they want to.
- When permission is withdrawn no further email may be sent to the subscriber.
GTSNZ clients must agree to comply with permission marketing
best-practices and all laws related to unsolicited email (SPAM). We
investigate any complaint that suggests a client is delivering
unsolicited commercial email and will take appropriate action should
they be in breech of this agreement.
We require all clients to allow
you to unsubscribe from periodic mailings such as newsletters. If you
can not unsubscribe by following the instructions in the email or by
contacting them such as phoning or writing to them, then please let us
know by emailing us at privacy@gtsnz.com

